Here you'll find useful resources created by the coalition members and friends of #RansomAware
Employee Reporting Prevents Widespread Ransomware Attack
Conditioning employees to be aware of phishing threats is the difference between experiencing an infection or two and a widespread ransomware attack.
Ransomware Protection Resource Center
It’s not easy to keep up with today’s threats. Now with Cofense, you’ll have a simple way to stay on top of emerging ransomware and phishing threats.
How to Prevent Ransomware
Learn how to prevent ransomware attacks before they happen. Dramatically sway the odds in your favor by following these tried-and-true best practices.
Phishing as a Ransomware Precursor
Over these years, phishing has been used to directly deliver ransomware often targeting individual machines for low ransom amounts. However, phishing is now most often a preliminary step in multi-step ransomware operations, rather than a direct delivery mechanism for ransomware itself.
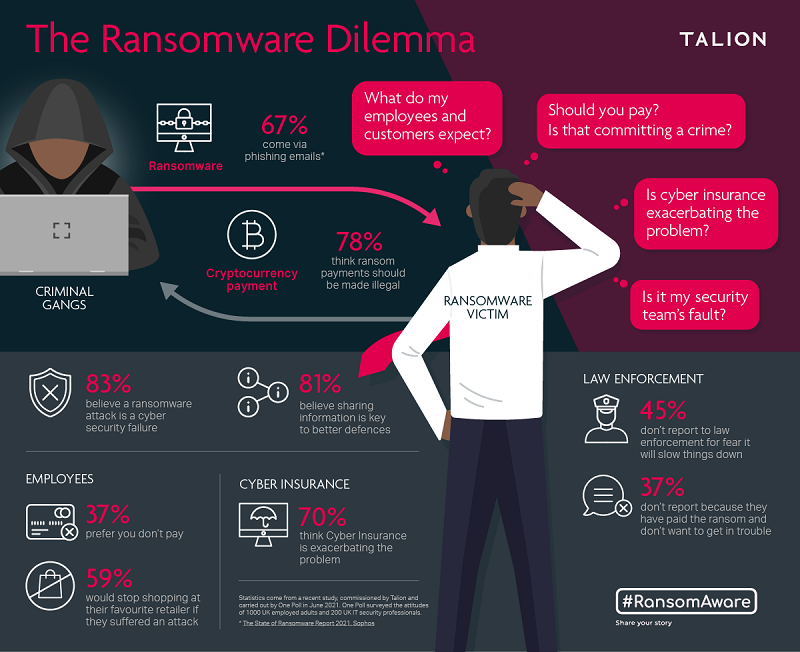
Ransomware Perceptions, 2021
A recent study, commissioned by Talion and carried out by One Poll in June 2021, surveyed the attitudes of 1000 UK employed adults and 200 UK IT Security Professionals.
Is Cyber Insurance Fuelling the Ransomware Crisis? Key Roundtable Takeaways
Recent Talion research shows that 70% of UK cybersecurity professionals believe insurance payments to companies that have paid a ransomware demand exacerbate the problem and cause more attacks. At this pivotal moment, there needs to be more openness, collaboration and standardisation, according to our expert panel.
Debate: Is Cyber Insurance Fuelling the Ransomware Crisis?
Watch the recording of this debate led by award-winning journalist, Oliver Pickup, as we discuss the increasingly controversial area of cyber insurance. With many blaming cyber-insurance policies for fuelling threat groups’ activity and encouraging more malicious actors to join the fast-growing ransomware industry, what is the future of cyber insurance?
A Ransomware Briefing for UK Businesses: Key Roundtable Takeaways
Cybersecurity must be a high priority for businesses large and small in 2021 – but most of all, as the law catches up with cyber criminals, there must be greater collaboration and knowledge sharing, according to our expert panel
The Threat of Ransomware to UK Businesses and How to Mitigate it
Watch the recording of this panel led by award-winning journalist, Oliver Pickup, bringing together some of the world’s most prominent ransomware experts to discuss pressing issues surrounding the onslaught of ransomware attacks currently threatening businesses.
Top 5 Ransomware Strains of 2021
Find our which ransomware gangs have been most prolific in 2021
Top 8 Ransomware Mitigation Tactics
Recommendations to help reduce the risk of falling victim to a ransomware attack
National Cyber Security Centre
What board members should know and what they should be asking their technical experts
To pay or not to pay
Flavia Kenyon outlines the increasing threat of ransomware cyber attacks on big business
Every breath you take, every move you make
Flavia Kenyon discusses the dangers of cyber espionage & global insecurity
A Ransomware Pandemic
Natalie Page, Threat Intelligence Analyst at Talion, discusses why we've seen such a massive rise in ransomware and what it means for businesses
National Cyber Security Centre
A new framework published by the Ransomware Task Force highlights the power of collaboration to address widespread cyber threats
Forbes Technology Council
Implementing An Effective Incident Response Strategy To Protect Against Ransomware - Keven Knight, COO at Talion
Forrester's List of Ransomware Resources
With ransomware continuing as a high-impact problem (with seemingly no end in sight), Forrester kindly put together some useful ransomware resources for security practitioners
Ransomware Costs: Beyond The Cash
We’re all too aware of the growing financial impact that ransomware attacks have on organisations. After all, it’s easy to talk in terms of dollars and pounds, but what about the under-talked about consequences of ransomware?
Ransomware Predictions for 2022
94% of organisations are concerned about the threat of a ransomware attack. We're helping organisations “step out of the dark” as we spotlight preparations you can bear in mind when approaching your security strategy this year.
Small Businesses Are Also At Risk Of Ransomware Attacks - Here's Why
Although small businesses have less revenue, less data and less employees, they are prime targets for ransomware attacks - here's why.
Employee Reporting Prevents Widespread Ransomware Attack
Conditioning employees to be aware of phishing threats is the difference between experiencing an infection or two and a widespread ransomware attack.
Ransomware Protection Resource Center
It’s not easy to keep up with today’s threats. Now with Cofense, you’ll have a simple way to stay on top of emerging ransomware and phishing threats.
How to Prevent Ransomware
Learn how to prevent ransomware attacks before they happen. Dramatically sway the odds in your favor by following these tried-and-true best practices.
Phishing as a Ransomware Precursor
Over these years, phishing has been used to directly deliver ransomware often targeting individual machines for low ransom amounts. However, phishing is now most often a preliminary step in multi-step ransomware operations, rather than a direct delivery mechanism for ransomware itself.
Ransomware Perceptions, 2021
A recent study, commissioned by Talion and carried out by One Poll in June 2021, surveyed the attitudes of 1000 UK employed adults and 200 UK IT Security Professionals.
Is Cyber Insurance Fuelling the Ransomware Crisis? Key Roundtable Takeaways
Recent Talion research shows that 70% of UK cybersecurity professionals believe insurance payments to companies that have paid a ransomware demand exacerbate the problem and cause more attacks. At this pivotal moment, there needs to be more openness, collaboration and standardisation, according to our expert panel.
Debate: Is Cyber Insurance Fuelling the Ransomware Crisis?
Watch the recording of this debate led by award-winning journalist, Oliver Pickup, as we discuss the increasingly controversial area of cyber insurance. With many blaming cyber-insurance policies for fuelling threat groups’ activity and encouraging more malicious actors to join the fast-growing ransomware industry, what is the future of cyber insurance?
A Ransomware Briefing for UK Businesses: Key Roundtable Takeaways
Cybersecurity must be a high priority for businesses large and small in 2021 – but most of all, as the law catches up with cyber criminals, there must be greater collaboration and knowledge sharing, according to our expert panel
The Threat of Ransomware to UK Businesses and How to Mitigate it
Watch the recording of this panel led by award-winning journalist, Oliver Pickup, bringing together some of the world’s most prominent ransomware experts to discuss pressing issues surrounding the onslaught of ransomware attacks currently threatening businesses.
Top 5 Ransomware Strains of 2021
Find our which ransomware gangs have been most prolific in 2021
Top 8 Ransomware Mitigation Tactics
Recommendations to help reduce the risk of falling victim to a ransomware attack
National Cyber Security Centre
What board members should know and what they should be asking their technical experts
To pay or not to pay
Flavia Kenyon outlines the increasing threat of ransomware cyber attacks on big business
Every breath you take, every move you make
Flavia Kenyon discusses the dangers of cyber espionage & global insecurity
A Ransomware Pandemic
Natalie Page, Threat Intelligence Analyst at Talion, discusses why we've seen such a massive rise in ransomware and what it means for businesses
National Cyber Security Centre
A new framework published by the Ransomware Task Force highlights the power of collaboration to address widespread cyber threats
Forbes Technology Council
Implementing An Effective Incident Response Strategy To Protect Against Ransomware - Keven Knight, COO at Talion
Forrester's List of Ransomware Resources
With ransomware continuing as a high-impact problem (with seemingly no end in sight), Forrester kindly put together some useful ransomware resources for security practitioners
Ransomware Costs: Beyond The Cash
We’re all too aware of the growing financial impact that ransomware attacks have on organisations. After all, it’s easy to talk in terms of dollars and pounds, but what about the under-talked about consequences of ransomware?
Ransomware Predictions for 2022
94% of organisations are concerned about the threat of a ransomware attack. We're helping organisations “step out of the dark” as we spotlight preparations you can bear in mind when approaching your security strategy this year.
Small Businesses Are Also At Risk Of Ransomware Attacks - Here's Why
Although small businesses have less revenue, less data and less employees, they are prime targets for ransomware attacks - here's why.