94% of organisations are concerned about the threat of a ransomware attack. This is no surprise when cyber criminals’ tactics are becoming more and more advanced, daring to overtake the capabilities of advanced security systems and infiltrate some of the most well-protected environments.
Understanding the direction of ransomware over the course of the next year will help organisations like yours “step out of the dark” as we spotlight preparations you can bear in mind when approaching your security strategy.
It may already be April, but it’s never too late to make improvements to your security posture.
Here are our 2022 ransomware predictions…
Ironically, in the prediction that cybercriminals will get smarter, they will lose their predictability; the constant updating of tools, procedures and tactics means it will be difficult for us to stay one step ahead. The advancement of technology has meant that ransomware has reached a new level – ransomware-as-a-service (RaaS) has meant that even the most amateur of cybercriminals can execute attacks with the use of already-existing ransomware tools from top ransomware threat groups, taking a cut of the ransom payment as a result.
However, cybercriminals aren’t necessarily getting smarter by advancing forwards in technology; FIN7 are an example of a threat group that have returned to old school tactics – some even from the nineties. Since antivirus is getting so good at detecting advanced methods, using old techniques is a smart method to catch victims off guard.
An example of this is the use of Right-to-Left Override (RLO), aimed to trick users into opening a file with a disguised extension. This non-printing Unicode character, mainly used to support Hebrew and Arabic languages, flips the characters and changes the text from English’s left-to-right to right-to-left. “HelloVade”, for example, with the Unicode character added as “Hello[U+202e]Vade”, would become “HelloedaV”. Victims would then open files believing them to be a .txt file rather than a corrupted .exe application.
Malicious actors have been adapting this technique as these attacks have become more and more detectable; now these files are often compressed into a .zip archive to bypass endpoint security technologies and increase chances of success.
Ransomware execution is currently at its most accessible; with ransomware-as-a-service (RaaS), anyone can get on board as an affiliate to execute ransomware attacks using the tools of larger threat groups. If skillset is no longer vital, it’s likely ransomware attacks will increase in prevalence as they become widespread.
Natalie Page, Threat Intelligence Analyst at Talion, shares her thoughts:
“My personal predication is that RaaS attacks will increase for two reasons.
The first being that Russia have trained a large number of low-level affiliates, who have been used to carry out cyber operations in support of the Russia side of the ongoing conflict against Ukraine. Once these operations subside and these trained affiliates are no longer needed, I believe these affiliates shall use this skillset to join the RaaS gangs. As a result of the recent Conti chat logs leak, it was found Conti affiliates earn an average of $1,800 per month, while the average Russian household brings in $540 per month, making it an extremely appealing lateral shift for these individuals.
Secondly, it has been speculated that Russia plan to retrieve funds lost to sanctions and the companies who have pulled out of Russia via ransomware attacks, and with previous multi-million-dollar ransom demands from Russian RaaS gang successfully paid, it is clear to see why this strategic method to retrieve funds could be an effective one.”
Organisations have to stay vigilant of growing ransomware, especially when global politics come into play. It seems that ransomware won’t stop until the risk outweighs the reward which, with continual improvements to cybercriminal techniques and the opportunistic angle of the global crisis, is unlikely to happen anytime soon.
Victims of ransomware attacks are less and less willing to pay ransom to decrypt files – attackers, therefore, are going to extreme lengths to convince them and increase their chances of getting paid. One of these techniques is no other than triple extortion.
Triple extortion is when a threat actor uses a combination of encryption and data theft to pressure victims to pay ransom demands, threatening to (1) publicly release stolen sensitive information, (2) disrupt the victim’s internet access and/or (3) inform the victim’s partners, shareholders or suppliers about the incident.
Cybercriminals are getting more and more creative with this, executing some of the following tactics:
One particular tactic has recently garnered greater attention – the role of cyber insurance in convincing organisations to pay the ransom fee. Ransomware groups are researching cyber insurance policies during the reconnaissance phase of the attack, calling up organisations they know have cyber insurance and giving companies guidance on how they can successfully retrieve their payment from the insurer after paying the ransom.
This is becoming a huge issue as insurers are arguably driving ransomware attacks by paying ransom demands since this is not yet illegal. Some have suggested that insurers should require minimum ransomware controls as part of any ransomware coverage to solve this problem, but we are yet to see this executed consistently across insurers.
Preparing your organisation in the fight against ransomware starts with understanding the trends and aligning your strategy, and we hope these 2022 predictions have been helpful.
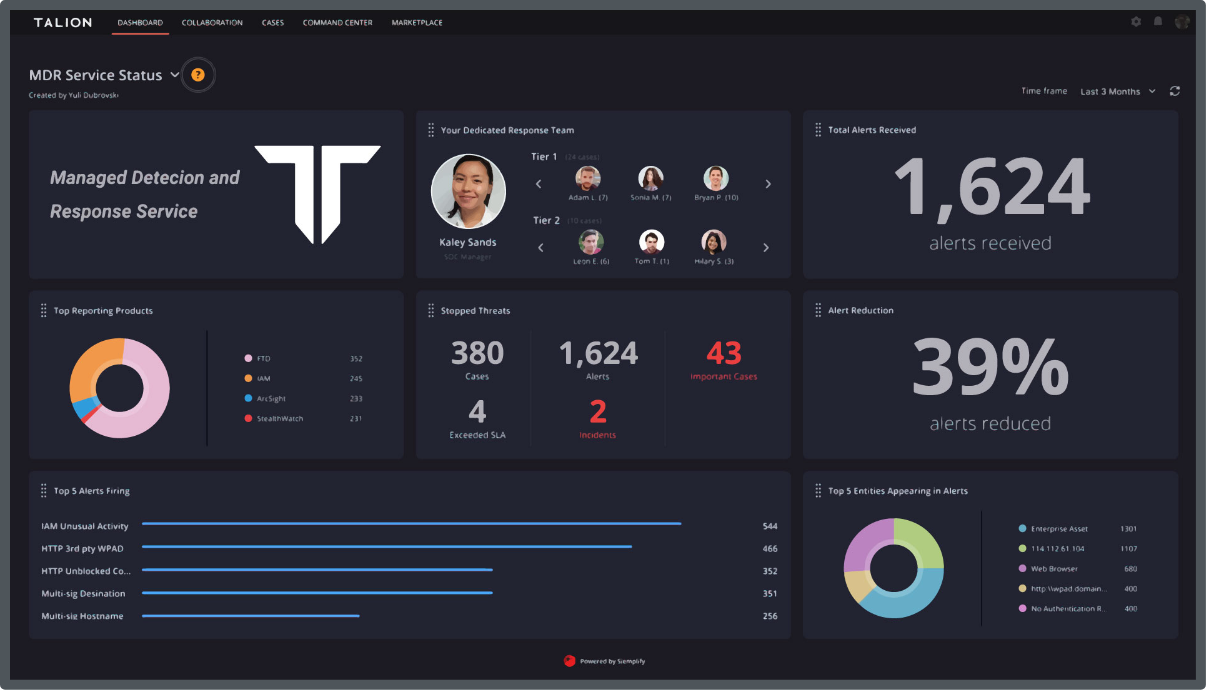
Ransomware attacks aren’t always as predictable as we want them to be, but with the help of Managed Detection and Response (MDR) services and a constant evaluation of your security posture, your company and employees can stay safe.
Read our Top 8 Ransomware Mitigation Tactics to learn more about protecting your organisation.
Call us directly and we’ll put you in touch with the most relevant cyber expert.
Not currently free to call? Give us a brief description of what you’re looking for by filling out our form and we’ll email you as soon as we can.
