It’s an age-old question but one still facing many Information Security teams when they are deciding how best to monitor and protect their IT estate.
The most important decision you will need to make is whether to build and operate the monitoring capability yourself or to outsource it. Key to this decision is whether you have the resources to design, implement and operate a 24/7 monitoring solution.
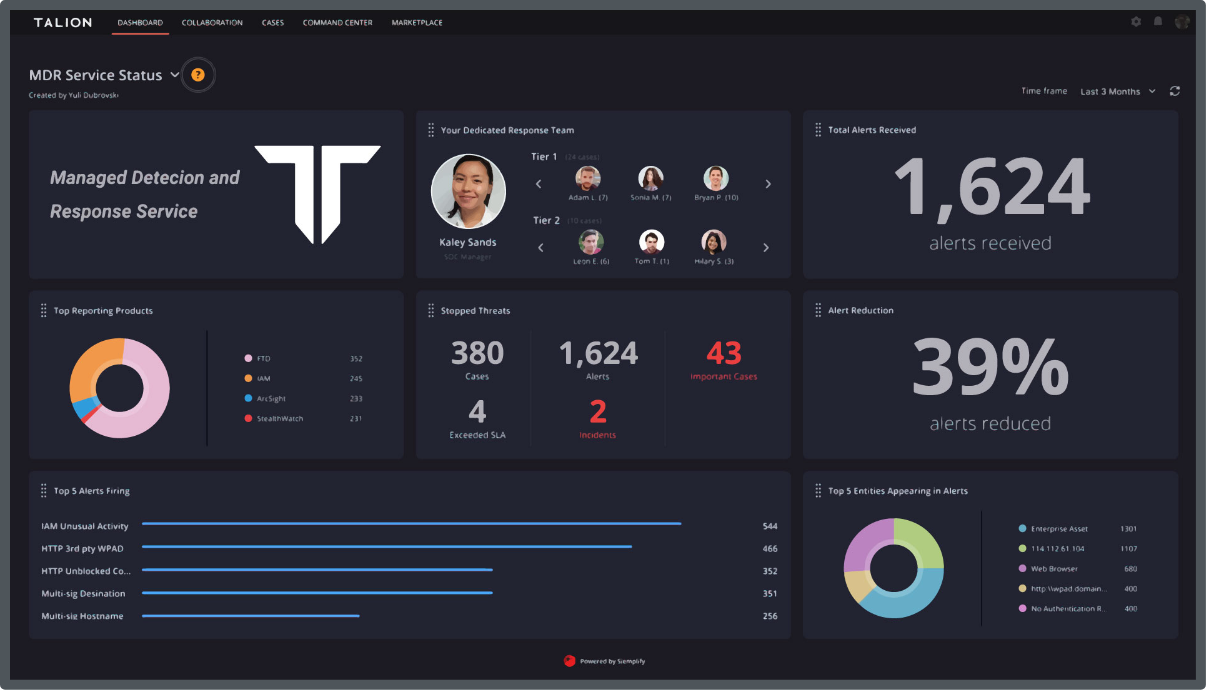
MSSPs operate in a competitive environment and in a market where MSS prices can vary by more than 100%, what you get may be quite different to what you expect. For example, a compliance-based MSS will generate alerts based on “out-of-the-box” rules with little information to help you respond, but a security-based MSS operating sophisticated rules and analytics will deliver to the client fully investigated security incidents with clear remedial action.
As Managed Security Solutions become more all-encompassing you also need to assess if you have the capability and capacity to integrate and manage multiple different products in your technology stack. A full-blown MSS will likely be offering the following in an integrated fashion:
Within each of these categories there is a whole swath of product on offer so the task of building your own solution is rightly a daunting one. If you decide to go down the path of procuring an MSSP, there are both strategic and cultural factors to consider:
Now you’ll need to understand your solution requirements
Talk to your IT architects and operations managers to identify the options for meeting your monitoring needs. The right answer depends on your organisation’s operational constraints. The main ones are:
Build or buy decisions made in the context of such operational constraints will be logically founded and defensible. In general, only the well-resourced organisations in regulated market sectors such as banks and energy companies choose to build their own monitoring capability. The rest of the market supports outsourcing. In both cases, you will need to find the right security partner to support you.
We provide consulting services to support you in building or improving your own monitoring capability. We can also provide threat detection products and outsourced management security services. If you would like to discuss how we can help you acquire an IT security monitoring capability that is right for your business, please contact us.
Call us directly and we’ll put you in touch with the most relevant cyber expert.
Not currently free to call? Give us a brief description of what you’re looking for by filling out our form and we’ll email you as soon as we can.
