Ransomware gangs are focusing on healthcare more than ever. With a 650% increase in ransomware attacks on medical facilities over the last year – the most significant jump in attacks by industry – it seems that healthcare systems are especially vulnerable.
There is an increased demand for resources due to COVID, the expansion of mobile apps to manage appointments, and the pressure of emergency staff who are under immense pressure with critical-decision making. For example, when it comes to malicious emails, is this at the forefront of staffs’ minds?
These are only a few of the cybersecurity challenges the healthcare industry are currently facing…
Health and medical facilities are known for holding huge amounts of sensitive data. From personal addresses to full medical records, it’s no surprise that cyber attackers benefit from bargaining with data that is so personal and revealing to our individual lives.
Interestingly, out of all industries, healthcare is most likely to pay the ransom fee, ranking first with 61% of organisations paying up to retrieve the decryption key. This is almost 20% more than the global average and has doubled from 34% in 2020. Could this be because healthcare data is so valuable (in both a monetary and personal sense), organisations don’t want to risk losing it, so they hand over the money?
A single healthcare record can sell for $250 on the black market – a value that’s considerably higher than credit card information, for example. It seems that organisations will do anything to prevent this from happening – to prevent both the violation of their patient’s records but also the ruining of their reputation.
Regardless of the fact that 65% of organisations haven’t retrieved all their data post-ransom, it still seems to be a popular choice when sensitive data is on the line.
Ransomware attacks are inevitably about exploiting weaknesses. Zscaler CISO Deepen Desai says modern ransomware attacks require a single successful asset compromise to gain initial entry, move laterally and breach the entire environment, and that “attackers are finding success exploiting weaknesses across businesses’ supply chains as well as critical vulnerabilities like Log4Shell, PrintNightmare, and others.”
These weaknesses are often identified in the healthcare industry through programs such as mobile health apps, where medical facilities typically lose full control over data, as it is left (quite literally) in the hands of the patient.
Endpoints must be thought of as start points – where the threat actor will strike first. With work devices and equipment no longer living solely under one roof, due to the increased flexibility of working from home since the pandemic, devices exist in their own autonomous environment where, essentially, anything can happen. Security can completely go out the window.
Cyber criminals often use phishing, identity theft and account takeover to obtain access to endpoints but even internet connection itself can be a vulnerability. Data must be monitored both in transit between devices and third parties but also when simply stored in your organisation’s servers. When best practices are overlooked and unnecessary people have access to sensitive information, that’s when secure data becomes insecure, and that’s when the business is at harm.
66% of healthcare organisations were hit by ransomware in 2021, up from 34% in 2020, and this is continuing to rise.
We’ve taken a look at two healthcare ransomware attacks from 2022 that have had detrimental effects:
Yuma Medical Center
On April 25th 2022, a ransomware attack was detected at the Yuma Medical Center, affecting 700,000 patients. Immediate action was taken to contain the attack and systems were taken offline to prevent further unauthorised access. However, prior to file encryption, a subset of files was exfiltrated from its systems, including names, Social Security numbers and health insurance information, affecting both current and former patients in Yuma County. As of yet, no ransomware threat group has stepped forward to claim responsibility.
CSI Laboratories
On February 12th 2022, CSI Laboratories fell victim to a ransomware attack where limited patient data was exfiltrated from its systems, containing patient names and case numbers, but even addresses, dates of birth, medical record numbers and health insurance information for a number of patients too. Whilst the nature of the attack has not been exposed, Conti ransomware gang have claimed responsibility and published a sample of the exfiltrated data on its data leak site.
Increase visibility
Like anything, the more knowledge you have, the easier and more effective it is to make an informed decision. Devices no longer remain solely on-premise in a single office, therefore having visibility of your office-endpoints and their networks helps you identify points of potential cyber infiltration. You can also invest in an attack surface monitoring solution that displays key vulnerabilities associated with cloud solutions within a private network.
Promote Cyber Threat Awareness
You can’t expect employees to just know cybersecurity best practices, and attack methods are constantly changing and updating – staying up to date is a priority. Whether sharing webinars or free cybersecurity resources, to hosting your own internal event days to tackle cyber issues head on, talking about cybersecurity is an essential starting point to reduce chances of insider threat.
For more advanced awareness on cyber threat trends, organisations may consider investing in Threat Intelligence to aid their security team in taking meaningful and relevant security action in the areas that are most at risk.
Invest In Security Software
At a bare minimum, we recommend organisations using software such as multi-factor authentication (MFA) to reduce security risk. This is often simple to set up and it’s estimated that up to 90% of cyber-attacks could be prevented with MFA enabled on endpoints and mobile devices.
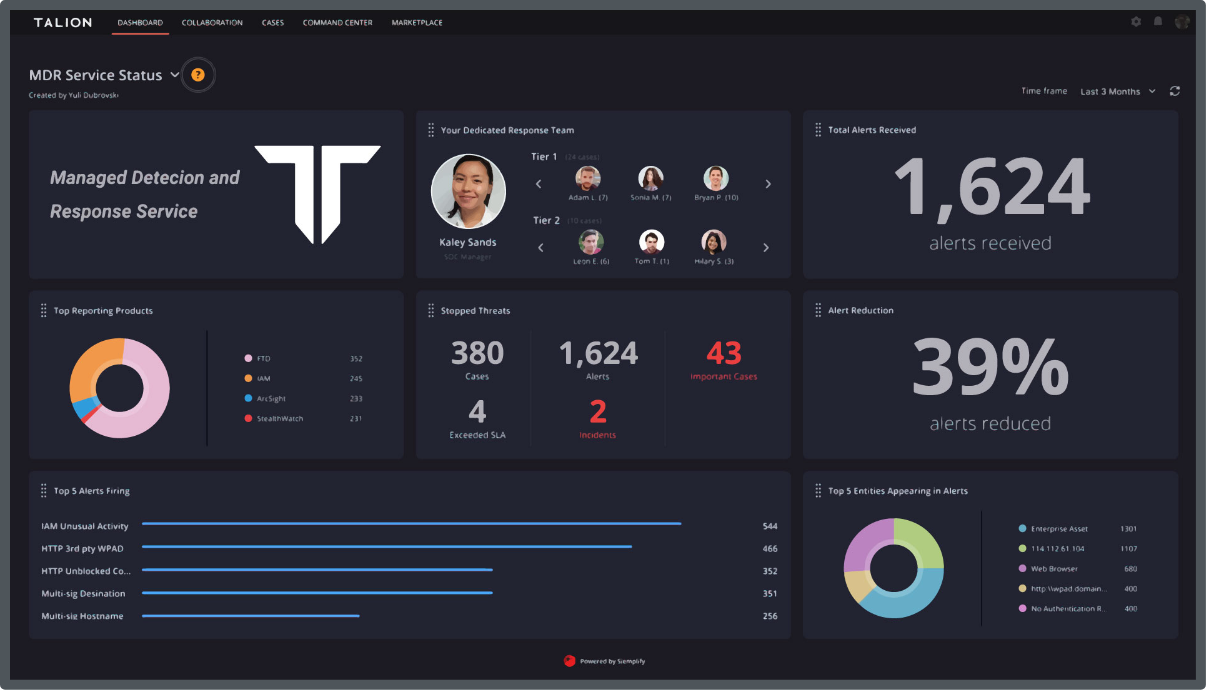
However, if organisations are looking for a suite of solutions tailored to their needs, investing in a Hybrid SOC or Managed Detection and Response (MDR) service can provide greater visibility and remediation of cyber threats, even managing security on your behalf if you wish.
Are you a healthcare organisation worried about the risk of ransomware attacks?
Reach out to us for advice, or join our #RansomAware community.
Call us directly and we’ll put you in touch with the most relevant cyber expert.
Not currently free to call? Give us a brief description of what you’re looking for by filling out our form and we’ll email you as soon as we can.
