Multinational technology conglomerate Cisco recently got hit with a data breach by ransomware gang Yanluowang who publicised a list of company files – proof that no organisation, no matter how large, is safe.
Whilst the details of the event are only now unravelling, the origin of it all began in May.
Here’s an insider scoop of what happened and who is really telling the truth.
Before the Yanluowang ransomware gang went public with Cisco’s files in August, there was talk of an initial hack in May – this was the beginning of the saga.
Talos Intelligence Group confirmed through a blog post that Cisco were first aware of a potential compromise on May 24th, although it was kept under wraps. This led to a confirmed data breach which was continually investigated by the CISCO Security Incident Response (CSIRT) team.
There have been suspicions raised by security leaders that Yanluowang is linked to “Evil Corp” (UNC2165) and FiveHands ransomware (UNC2447) since the Tactics, Techniques and Procedures (TTPs) of the attack closely mirror one another, including infrastructure that matches a Conti ransomware affiliate which has been seen deploying Hive and Yanluowang ransomware payloads before.
However, it seems the evidence is still unclear and there is room for debate.
Fast forward to the present moment and the public are well aware of the data breach that’s gone down.
Yanluowang, who have likely chosen their name by referencing Yanluo Wang (a Chinese deity who was said to be one of the Kings of Hell), have shared their Cisco point of access – an employee’s VPN account. The hacker gained control of a personal Google account, accessed the credentials saved in the victim’s browser and through a series of sophisticated voice phishing attacks, under the guise of various trusted organisations, convinced the victim to accept multi-factor authentication (MFA) push notifications which granted the attacker access to the VPN.
After this, the attacker was able to do all sorts of damage:
Whilst Cisco initiated a company-wide password reset and the attacker was successfully removed, they repeatedly attempted to regain access in the following weeks. However, this was of no such success.
So, what happens when a ransomware gang says one thing, and the targeted company say another?
It’s hard to know what’s really going on.
According to Yanluowang, they’ve stolen thousands of Cisco’s files amounting to 55GB, including classified documents, technical schematics and source code. However, this is a big claim to make with very little evidence.
Cisco, on the other hand, have publicly announced that the stolen data was completely non-sensitive and the attack was contained well before Yanluowang had the chance to start encrypting systems.
“We have no evidence to suggest the actor accessed Cisco produce source or any substantial access beyond what we have already publicly disclosed.” – Cisco
As a result, Cisco are running as usual with no impact to the business, which would be hard to do if Yanluowang had indeed stolen their sensitive files.
It is likely Yanluowang are, therefore, exaggerating the result of the cyberattack, perhaps in order to damage the reputation of Cisco or create a sense of mistrust amongst their customers.
We’d like to highlight the importance of companies speaking up about their challenges with ransomware – it is only with public acknowledgement and sharing of resources that the fight against ransomware will get easier.
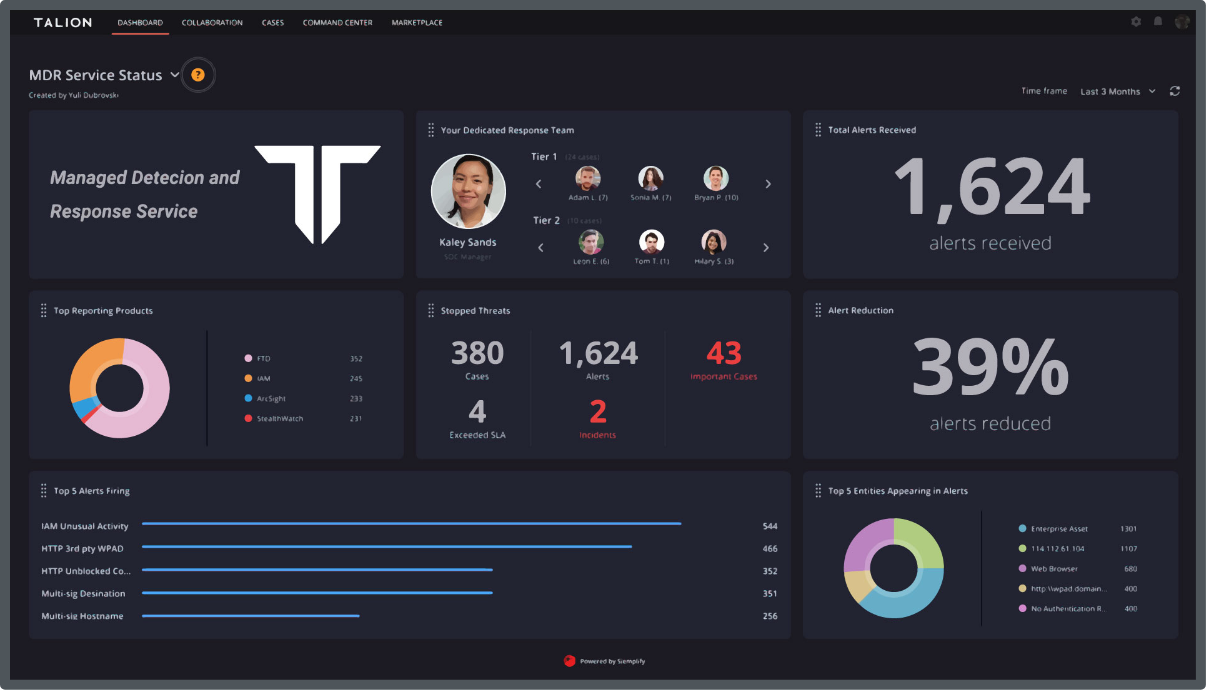
There are a number of ways companies can tackle the challenges within their security strategy, from moving past reliance on legacy solutions (which can’t keep up with today’s advanced hacker techniques), improving awareness and visibility internally amongst employees and looking to outsource security services to ease the burden of alerts within security teams.
Evaluate your current processes and find what works best for you.
Reach out to us if you’d like to have a further chat – you can contact us here.
Call us directly and we’ll put you in touch with the most relevant cyber expert.
Not currently free to call? Give us a brief description of what you’re looking for by filling out our form and we’ll email you as soon as we can.
