-

Legal
A Fraudster’s Goldmine
Read more Close -

Healthcare
At Risk of Ransomware
Read more Close -

Defence
Classified Information
Read more Close -

Forestry
Cybersquatting
Read more Close -

Technology
Double Agent
Read more Close -

Legal
Imitation Games
Read more Close -

Aviation
Protest Foiled
Read more Close
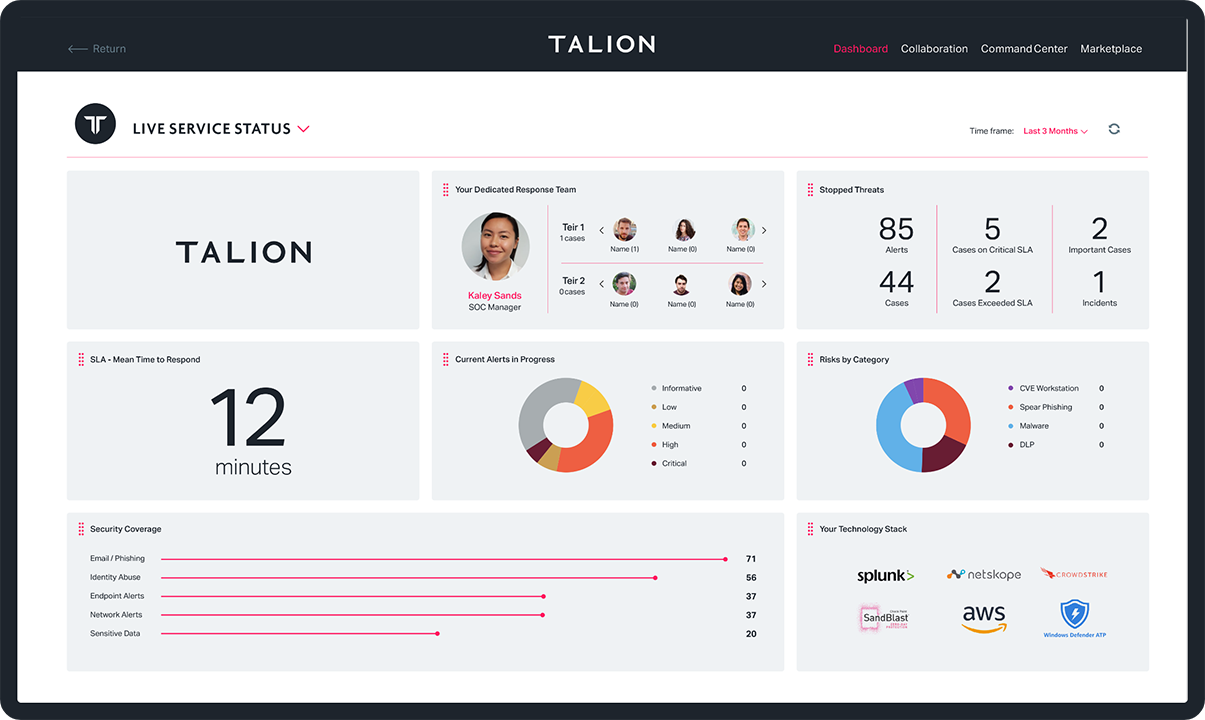
Serious Internal Misconfiguration
Poor internal processes can leave businesses seriously exposed to attackers. While conducting Open-Source Intelligence (OSINT) for a client in the legal sector, we found that confidential emails were being systematically uploaded to a malware repository. The emails included .wav recordings of conversations firstly between clients and the business, and secondly between the business and the bank.
The recordings exposed personal information, banking passwords, passphrases and financial information. We supported our client in removing all the files from the site before the information could be found and misused.
Outcome
Left/Right of breach
Organised Criminal Gang
Part of our Open-Source Intelligence (OSINT) work is about monitoring the online footprints of our clients. When delivering a security report for a client in the healthcare sector, we highlighted how their corporate network was vulnerable to a ransomware propagation attack.
Potentially highly serious, this type of attack could have blocked their network indefinitely, demanding a sum of money for its release. In making the client aware of this vulnerability, they were able to update their network and tighten internal security.
Outcome
Left/Right of breach
Serious Internal Misconfiguration
Internal mistakes can be just as damaging as external attacks. This was the case when we spotted a user connecting an unauthorised disk to the corporate network. The disk contained highly classified information and should only have been connected to an air-gapped network.
We informed the client, who seized the disk and opened an investigation, avoiding any serious reputational damage.
Outcome
Left/Right of breach
Serious Internal Misconfiguration
During routine monitoring, we found that our client’s industrial control system was highly insecure, potentially granting admin control and access without authentication to any third party. What’s more, passwords for all users were universally visible, potentially opening up further avenues for cyber attack.
We notified the client, who then liaised with their system provider, insisting that security measures were updated and best practices were implemented.
Outcome
Left/Right of breach
Criminal Threat Actor
Proactive security monitoring prevents major incidents before they happen. And this was the case when we spotted an unknown domain registration that appeared to be hijacking our client’s URL, a mode of attack also known as typosquatting. Further research told us the new registration didn’t match our client’s registrar or comply with their corporate process.
Within 24 hours of the unknown registration, the client was informed and the issue was resolved before the attackers could cause any damage to the client’s business.
Outcome
Left/Right of breach
Insider Threat
Security threats can come from all angles. When a technology client raised concerns regarding a particular employee, we added the user onto the enhanced monitoring list. We then observed the individual downloading 1904 files onto their personal OneDrive in a 30-minute timeframe.
We filed our report to the client, who dealt with the issue internally, avoiding a potentially damaging case of corporate espionage.
Outcome
Left/Right of breach
Criminal Threat Actor
Malware repositories are a valuable resource for hackers. While working for a client in the legal industry, we found that hackers had used malware to obtain a legitimate email chain between our client and a third party company. This gave the hackers access to names, job titles, project details and more.
Their next move was to create fake domains imitating both our client and the third party. From there, they sent emails between the two domains requesting payment details. We identified the threat before either company was duped into revealing financial information, preventing a significant loss of funds and damage to our client’s reputation.
Outcome
Left/Right of breach
Activists
Social media monitoring is a key phase of our Open-Source Intelligence (OSINT) service. While gathering intelligence for a client in the aviation industry, we identified an activist group planning a physical protest via social media. The Metropolitan Police didn’t yet have this information.
Our regular intelligence updates enabled the client to monitor the situation and disrupt the protest by intervening accordingly, preventing any reputational damage.